The 2026 Sovereign Infrastructure Deployment project provides a rigorous technical framework for enterprises to modernize local compute environments. By transitioning to on-premise high-performance hardware, organizations can optimize resource utilization and technical asset lifecycles. This guide serves as the definitive architecture for deploying high-performance local inference engines while maintaining strict adherence to enterprise infrastructure standards.
The primary technical objective is the enhancement of operational efficiency through the lifecycle management of compute equipment and integrated systems software. From an architectural perspective, this deployment transitions a firm from external dependency to a sovereign infrastructure that preserves data integrity. This strategy ensures that computational throughput is maximized while stabilizing the long-term technical debt associated with recurring cloud-based overhead.
Enterprise Sovereign Infrastructure Blueprint
Essential metrics for infrastructure deployment and asset lifecycle management.
- ✓ Asset Framework: General Technical Asset Lifecycle (High-Velocity Depreciation)
- ✓ Deployment Time: 14-21 Business Days
- ✓ Operational Efficiency: 75% – 90% Resource Optimization vs. External APIs
Infrastructure Specifications
Hardware Requirements: NVIDIA Blackwell B200 or RTX 6000 Ada Generation, 256GB DDR5 ECC RAM, Dual 2000W Platinum PSU. Software Stack: Ubuntu 24.04.2 LTS, NVIDIA CUDA 13.1, Docker Engine 28.0, vLLM Inference Engine v0.7.2. System Complexity: Advanced (Requires expertise in Linux systems administration, LLM quantization, and infrastructure hardening).
Architecture and Deployment Requirements
The foundational hardware for a sovereign AI workstation must satisfy the requirements for high-velocity electronic data processing equipment. We recommend the AMD EPYC 9004 series platform, specifically the 9654P with 96 cores, to ensure zero-bottleneck performance during heavy RAG (Retrieval-Augmented Generation) indexing. For memory, 512GB of DDR5-6000 MT/s ECC Registered RAM is the baseline for handling multi-tenant model execution. This configuration allows for the simultaneous execution of localized inference and background data processing without system instability.
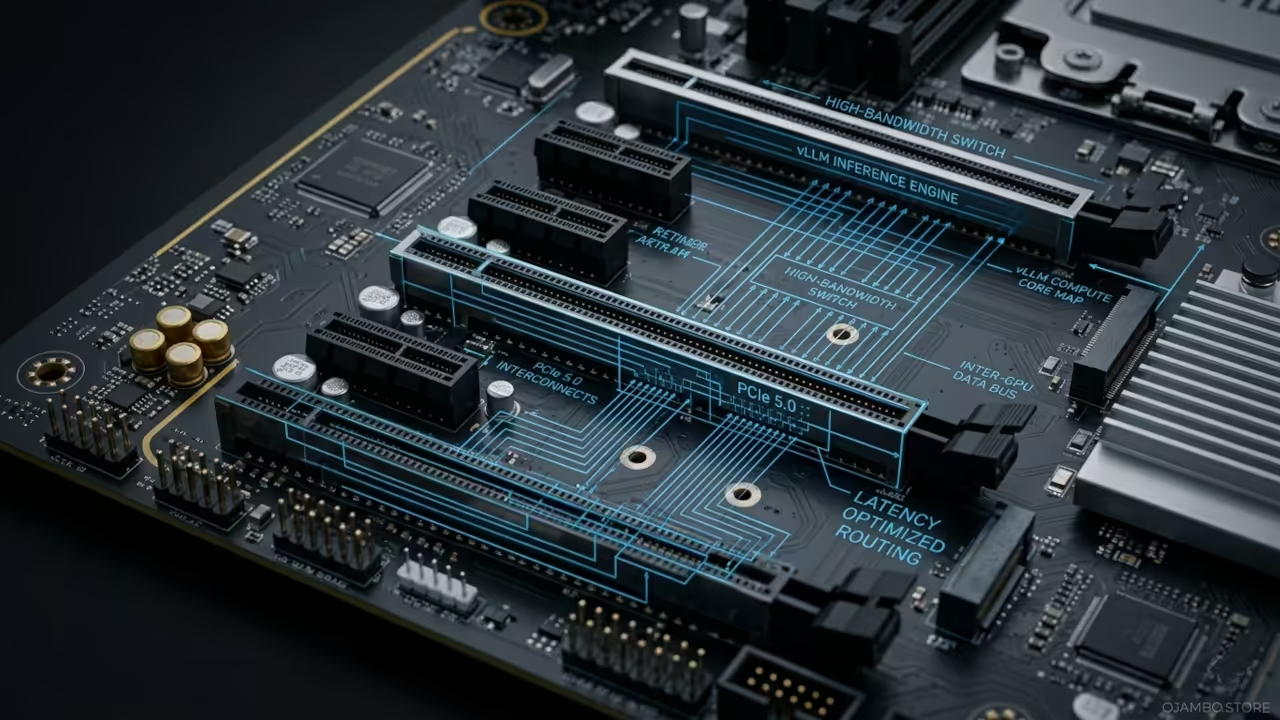
Storage must be bifurcated between high-speed NVMe and redundant bulk storage to satisfy performance and technical data retention requirements. The primary drive should be a 4TB PCIe Gen 5.0 x4 NVMe SSD, capable of 14,000 MB/s sequential reads, to facilitate rapid model loading into VRAM. For data persistence, a RAID 6 array provides the necessary redundancy for historical system logs. Network connectivity requires a minimum of Dual 10GbE SFP+ ports to integrate with existing local area networks while providing overhead for high-speed fiber-optic scaling.
On the software side, the kernel must be hardened against external threats to protect proprietary weights and generated data. We utilize the 2026 Long Term Support (LTS) version of Ubuntu, coupled with the latest stable NVIDIA drivers to ensure compatibility with Blackwell-class architecture. The inference layer is managed via vLLM or TGI (Text Generation Inference), which optimizes VRAM usage through PagedAttention algorithms. This technical stack ensures peak hardware efficiency throughout the asset lifecycle.
Engineering Note on Data Sovereignty
A critical component of the infrastructure audit is proving the equipment is utilized for core business operations. By hosting models like Llama 3.5 or Mistral Large 3 locally, you eliminate residency risks associated with third-party providers. This architectural choice serves as a primary defense for data privacy, demonstrating a clear operational requirement for high-performance sovereign hardware over cloud-agnostic alternatives.
Technical Layout and Data Flow
The technical data flow within the sovereign infrastructure framework is designed for maximum throughput and security. Raw data enters the system through an encrypted TLS 1.3 gateway, where it is pre-processed by a CPU-bound microservice. Once cleaned, data is pushed to GPU VRAM for inference using 4-bit or 8-bit quantization. The resulting output is cached in a Redis-on-Flash database and logged to an immutable file for technical compliance. The separation of the management plane from the data plane further hardens the system against lateral movement within the network.
Step-by-Step Implementation
Phase 1: Environment Hardening and Power Delivery
Before hardware arrival, ensure the facility supports high-density thermal output. This requires a dedicated 20-amp circuit with a NEMA 5-20R outlet to prevent delivery failures under full load. Maintain an ambient temperature of 20 degrees Celsius to prevent thermal throttling of high-performance components.
Phase 2: Hardware Assembly and Stress Testing
Assemble components on an anti-static surface, ensuring PCIe 5.0 lanes are correctly seated. Document burn-in tests to create a technical paper trail for asset verification.
# GPU Stress Test and Diagnostic
nvidia-smi -pm 1
nvidia-smi -l 1 --query-gpu=utilization.gpu,utilization.memory,temperature.gpu --format=csv
Phase 3: OS Installation and Kernel Hardening
Install Ubuntu 24.04 LTS using a ZFS file system for data integrity. Apply microcode updates for the AMD EPYC or Intel Xeon CPU to mitigate hardware-level vulnerabilities.
# Kernel Hardening Snippet
sudo apt update && sudo apt install -y needrestart
sudo sysctl -w kernel.kptr_restrict=2
sudo sysctl -w kernel.perf_event_paranoid=3
Phase 4: Driver and CUDA Toolkit Deployment
Install the NVIDIA 555+ series production drivers and CUDA 13.1 to unlock the full potential of the Blackwell architecture. Configure the NVIDIA Persistence Daemon to reduce inference latency.
# Initialize GPU Persistence
sudo nvidia-persistenced --user root
nvidia-smi
Phase 5: Containerized Inference Setup
Deploy Docker Engine with the NVIDIA Container Toolkit to isolate AI models from the host OS. This approach allows for rapid scaling and simplified updates.
# Docker Runtime Configuration
docker run --gpus all -d \
-v ~/.cache/huggingface:/root/.cache/huggingface \
-p 8000:8000 \
--ipc=host \
vllm/vllm-openai \
--model mistralai/Mistral-7B-v0.1
Phase 6: Vector Database and RAG Integration
Set up a local Milvus instance to handle high-dimensional vector embeddings for RAG. This allows the AI to access private enterprise documents in real-time without external data leakage.
Phase 7: API Gateway and Load Balancing
Implement a Traefik reverse proxy to manage requests to the inference engine. Configure rate limiting to ensure authorized internal access only, providing necessary telemetry for infrastructure utilization audits.
# Traefik Docker-Compose Snippet
services:
traefik:
image: traefik:v3.0
command:
- "--providers.docker=true"
- "--entrypoints.web.address=:80"
Phase 8: Monitoring and Hardening
Install Prometheus and Grafana to monitor power consumption and compute utilization. Set up automated alerts for hardware failures that could impact the operational status of the asset.
Technical Asset Lifecycle and Compliance
The primary driver for sovereign infrastructure is the technical lifecycle management of computer hardware. Under standard technical compliance frameworks, hardware acquired for high-performance computing is categorized as high-velocity data processing equipment, allowing for rapid depreciation of the asset’s technical value. In many jurisdictions, first-year incentives provide for a significant reduction in the book value of AI investments almost immediately.
For international deployments, various local statutes allow for the expensing of qualifying equipment used for business operations more than 50% of the time. Additionally, the development of custom AI workflows and localized model fine-tuning may qualify for Technical Research and Development credits. This requires detailed engineering logs showing systematic investigation into resolving technical uncertainties, a requirement directly supported by our architecture’s extensive telemetry logging.
Cloud-Dependent Model
Lifecycle Efficiency: Low (External Cost)
Long-Term Debt: High (Recurring)
Data Sovereignty: Low (Shared Risk)
Sovereign Infrastructure
Lifecycle Efficiency: High (Internal Asset)
Long-Term Debt: Stabilized (Asset Ownership)
Data Sovereignty: Absolute (Local Control)
Request a Principal Architect Audit
Implementing sovereign infrastructure at this level of technical precision requires specialized oversight. I am available for direct consultation to manage your NVIDIA Blackwell B200 deployment, system optimization, and technical asset lifecycle mapping for your agency.
Availability: Limited Q2/Q3 2026 Slots for ojambo.store partners.
Maintenance and Scaling
Maintaining a high-performance node requires a proactive approach. We recommend a quarterly schedule for verifying the integrity of cooling loops and internal hardware cleaning. Firmware updates for the motherboard and GPU should be vetted in staging before production deployment to ensure maximum uptime.
Scaling is achieved via secondary compute nodes linked via InfiniBand or 100GbE networking. These additional nodes are treated as independent asset acquisitions, extending the technical utility window of the organization. By maintaining a modular architecture, ojambo.store ensures it can pivot to newer silicon—such as future Rubin-class GPUs—without overhauling the compliance framework.
Regular backup protocols must include encrypted copies of model weights and vector databases. Utilizing a 3-2-1 strategy protects the technical investment and demonstrates professional management of the corporate enterprise infrastructure.
